Hannes Geldenhuys
Feb 18, 2026
Platform & Infrastructure
The Technical Debt Nobody's Checking: Why We Built the Moodle Site Integrity Tester
Most Moodle installations run for years without anyone checking the basics.
Not because IT teams are careless. Not because security doesn't matter. But because there's never been an easy way to audit what's actually exposed to the internet.
After managing Moodle for universities across the UK, US, and South Africa for 15 years, we kept seeing the same patterns:
Exposed version numbers that tell attackers exactly which exploits to use
Missing security headers that leave doors open
Backup files and configuration files sitting in publicly accessible directories
Misconfigured HTTPS that undermines the entire security posture
These aren't edge cases. They're what happens when a platform runs in production without dedicated security oversight.
The "IT handles it" assumption
In most institutions, nobody owns Moodle security explicitly.
Academic departments assume central IT is monitoring it. Central IT assumes the platform is low-risk because it's "just" a learning system. DevOps teams focus on uptime, not security hygiene.
The result? Nobody checks. For years.
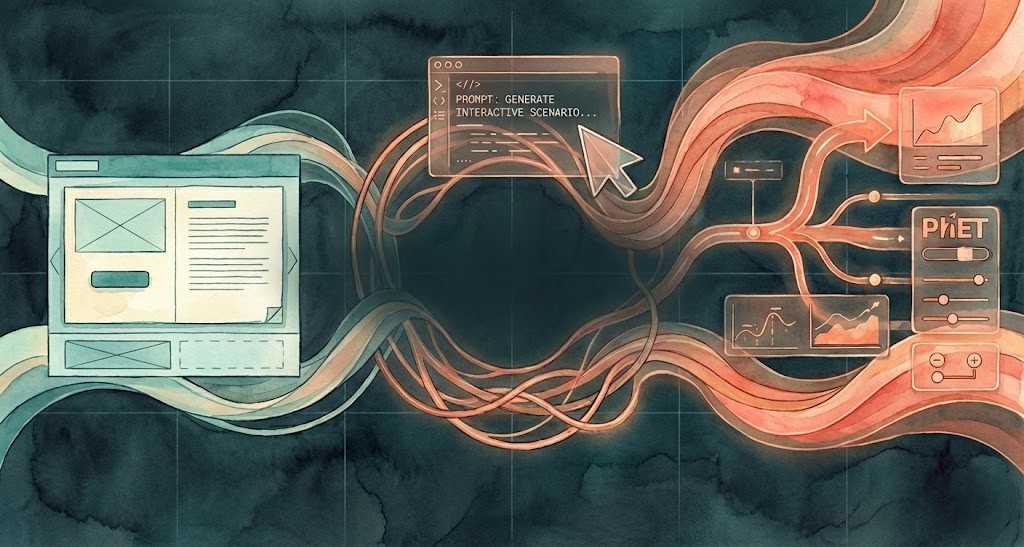
What the Moodle Site Integrity Tester does
We built a free tool that makes it trivial to audit any public Moodle installation in 30 seconds.
It checks:
HTTPS & TLS configuration — certificate validity, protocol versions, HSTS headers, mixed content
Security headers — CSP, X-Frame-Options, X-Content-Type-Options, Referrer-Policy
File exposure — detection of exposed .git directories, .env files, SQL dumps, backup archives
Version hygiene — whether your Moodle and PHP versions are being broadcast to potential attackers
Infrastructure — directory indexing, server software disclosure, admin endpoint exposure
The scan is completely non-intrusive. Read-only checks against publicly accessible endpoints. No login required. No data stored unless you opt in.
Why this matters
Technical debt is invisible until it isn't.
A misconfigured Moodle instance won't cause problems day-to-day. But when a security audit happens, or a breach occurs, or a compliance review surfaces gaps, the costs escalate quickly.
The institutions we've worked with don't lack expertise. They lack visibility. They're running platforms that were set up years ago, by people who've since moved on, with security configurations that haven't been revisited.
This tool gives you that visibility in 30 seconds.
Try it yourself
Run a scan on your own Moodle: security.webblms.com
If the results are sobering, that's normal. Most institutions are carrying more technical debt than they realize.
And if you'd rather hand the whole problem to someone who's been doing this for 15 years? Get in touch. We'll handle it.
Share this article: LinkedIn | Email
Similar Blogs
Stay close to the thinking
Occasional notes on university delivery, governance, and how institutions create space to move faster.
No marketing emails. Just thoughtful updates when there’s something worth sharing.